Satellite Internet Crime Traces: Forensics
Challenges and Innovations
Author:
Mr. Srimanta Mondal
e
all of are just waking up in the morning feeling crazy and lazy then suddenly
remember where is my phone or laptop etc., and we’re going to find it. Now
start our mission, everybody knows that what I am talking about, that yes just
scrolling Instagram, Facebook, Twitter and many more social media platforms.
And obviously checking WhatsApp massages for our daily and priority bases. Then
you clearly think yes, we are live in 21st century. The era of The
Digital World[1].
Figure
1:
Earth Before the Machine and after the Crime
|
Whenever
we are thought about this digital world, we can see the revolutionary change of
the world. Till the start our unstoppable journey from primordial soup to
pre-digital civilization[2]. Behind the story there is not only the
journey of revolutionary change of the digital world, advance technology
development. But there is something different way I have to tell all of you, my
endless journey in this field of study with all of experience. The Story of Earth Before the Machine and
after the Crime, Crime on Satellite Technology: Challenges and Innovations
in Forensics. Whenever I see the
earth, it’s a long time, almost Five billon years ago, a silent sphere of
molten rock spun in the emptiness of space, destroyed by meteorites and stirred
by the volcanic fury, in that time earth was no place for life[2]. But time, continuously evolving itself
with had patience, nature’s is a greatest engineer who create the life and
change itself which we are see the living things on earth. For millions of
years, the journey from it’s started with cloud vapors on the surface, to
today’s life sparked. It’s defined the greatest mind of science. In the warm
shallowed of Earth’s ancient, a small and simple molecule turned into a big and
complexing living beings, a grate transformation of the architecture[3]. Over passing years of years, evolved many
creatures and time over time humans are transformed into the brilliant creature
on the world. They are making weapons for collecting their food, to they are
making homes for live. Over time passes, humans are building some grate
civilization, one of them like Indus valley civilization, Egyptian
civilizations and others[3]. Curve their existence into stone tablets
and clay bricks[1].
These societies invented
some greatest monumental ideas, these are main reasons of our today’s evolution
and make the world digital, these monumental achievements like law, astronomy,
mathematics and philosophy[1]. In that time, humans are slowly becoming
monster’s for achieving the rule of world, that time had not any internet or
computer, but many extraordinary thinkers are creating several inventions for
the war, or the king who want to live thee life as luxurious way, or someone’s
create inventions for good welfare[2], [3].
Rise of Orbital
Cybercrime and the Collapse of Traditional Boundaries:
Figure
2:
The Evolution technology, also step on the crime.
|
Past
years of long journey, humans creating several inventions to achieving their
goal or fulfill their passion with using human intelligence and excellency. But
somehow this is the reason we are going to that path, what we are not expecting
“Crime”. Whenever we think, humans
are just evolving and trying to build a better future for the brightest world,
as soon world faces some crucial incident for break or destroy their dream. In
the past few years journey, the first technology invented by humans that is
considered to be “Stone tools” maybe it’s far from 4 million year ago to then
humans invented a revolutionary technology that called “computer”[4]. Around
1930s the first electronics computer was invented and the first business
computer in 1950s in the world. After that the internet conceived in the late
1960s with the development of ARPANET, which was initially invented for limited
used, as military or governmental use[5]. Then human thought why not we are connected
all over world interconnected way for fast communication process, then we are
slowly achieving our today’s fast and secure internet medium technology, where
we are connected our family, friends, office, stranger peoples, in country and
out of the country communication. But
who thought, that is the beginning of the end of human world, where humans
themselves have become the causes of one another's enemy, carrying out such
works with the help of advanced technology and internet. And that is the
beginning of crime. Today I am going to tell you about one such advanced crime
which is done with the help of satellite. My topic of discussion is going to be
how satellite crimes happen, how is the investigation of cyber forensics done,
which steps are implemented in it, and which challenges come in it and how does
our cyber forensic expert team handle it[4].
In
the early days of the internet, and its connectivity are comparatively short
range, so it will be advantage of crime investigation in short range geographic
location areas[6]. In that time there was highly possibility
if any attack originating from within inside a country, that could easily trace
via internet service providers, local IPs, physical logs or using server
metadata. That will help on finding clue on investigation to catch criminals.
But today, the world evaluates their technology[5]. The futuristic solution came over the
global ecosystem has begun to ascend into the stratosphere quite literally. Where
we are created isolated communities and connecting astronauts, and that is the
main aspect it became a central feature of the modern digital world. But while
it brings huge benefits for human on daily work, remote education,
communication, telemedicine and disaster recovery, but it has also opened a new
door for cybercriminals activity that create more challenges for traditional
digital forensic investigation frameworks[4], [5].

Figure
3:
Digital Forensic Investigation, Orbit Exploration.
|
At
the era of revolutions there are many commercial satellites provide internet
such as SpaceX’s Starlink, OneWeb, and Amazon Project Kuiper, which is offer
their users high speed and low latency internet access from anywhere on the
Earth through a constellation of low earth orbit (LEO) satellite[7]. These internet providers are enhanced
their infrastructure for managed entirely over terrestrials’ network. This
means its cover their connection most of rural villages, or it can be middle of
the ocean, or on the battlefield[8]. That’s the loop hole, some malicious actors
try to bypass their security local surveillance and perform attack, they can
confuse investigator, and create blind spot across the border to exploit
jurisdictional matter[6]. Just remembering a hypothetical scenario
of case where a ransomware group operating their mission of a conflict zone in
northern Africa[7]. As we know, Starlink just launching their
satellite in 2019 and significantly expanded their services globally,
particularly provided their services in where internet infrastructure is limited,
by 2022-2024[8]. During these time period some cases are
reported on misuse of Starlink network through sophisticated C2 and evasion
tactics they are perform criminal activities to gaining unauthorized access,
using a gray-market Starlink terminal to launch attack against high-value
European industrial targets[9]. The attackers group mask their true
location and hide their all local detection mechanisms, via the satellite network
by routing command and control instruction. When forensic research team respond
to the attack location and trace the IPs, they find out an endpoint which are
linked to a ground station in Germany, that are completely disconnected from
the original source origin of the crime[4], [8]. What follow is a month of long
international legal efforts and investigation to obtain partial logs, which are
anonymized themselves and inconclusive. In this case of scenario, there is no
traditional forensic trails exist, no local router logs, no telecom records, no
physical infrastructure[10], [11]. Here are questions come, how do forensic researcher team investigate
on that case in any of other future cases?

Figure 4:
New challenge for Digital Forensic. Orbital Cybercrime, by satellite
technology
|
This
no longer hypothetical. Over the past two years, documented that incident have
demonstrated the utility of satellite crime operations, that ranging from
remote cryptocurrency mining in the arctic circle to illicit drone operations,
to digital case of extortion campaigns launched from offshore location[10]. The appeal to criminal is clear: that
the probability of ground terminals, there clearly visible the difficulty of
this type of case scenario, and the technological novelty so that even many
professional forensic researcher or experts are unprepared to address on this
type technological crime. The major or it can say core problem for
investigators facing critical situation in the shift terrestrial traceability
to complex traceability orbital anonymity[10], [11]. In the traditional forensic
investigation, most important part is established a timeline paramount. So,
Investigator work through timestamps, geolocation records, log data, and
physical hardware analysis to reconstruct the sequence of actions involved in a
breach or digital crime[10]. But here is a main problem occur where satellite
internet fundamentally disrupts this model. Because many of the satellite
internet system use dynamic IP pools shared among multiple users, logs point
not to a single device or user, but to a network of hundreds. Because of the
ground system terminal are operated by highly mobile environment that including
car, boat, or even moving aircraft, that the physically link to ground
geographical location become tenuous. Moreover, the satellite communication
chain typically routes data through a series of relays, communicate multiple
continents, before existing into the terrestrial internet, that’s making packet
untraceable and create nightmare of international jurisdictions and incomplete
transparency[12].
Here
is the most complex complication is the lack of forensic hooks. There is most
of the satellite internet providers do not provide built-in packet monitoring,
end point attribution, or real-time logging accessible to law enforcement. Sometime
even when logs do exist, they are often retained for minimal periods of time,
and inconsistently timestamped, also inaccessible without extensive legal
cooperation[13]. In some country in the world, there is
simply not any law mandating such forensic cooperation from private space-based
ISPs. As a result, investigator find themselves facing digital blackhole, crime
that exist in digital form, but they are do not doing anything because these
crimes which are not any trace remains. This is the place, where the forensic
community must rise to facing new challenges. Here we are the witness to birth
of a new breed of cybercrime[10]. It’s called “Orbital Cybercrime, by satellite technology”. And the tools, legal
frameworks, and investigative mindsets that sufficed for land based digital
forensic already falling short[12]. In the future of forensic investigation
must look upward to the skies, to the satellites, and to the space between them[12], [13].
A
New Forensic Battlefield — Challenges That Orbit the Law:
Figure
5:
Earth’s satellite internet infrastructure in low Earth orbit (LEO).
|
The rapid development of satellite
internet infrastructure has not only opened the beneficial sources to every user
but it can also to threat actors who exploit its distinct architecture to
commit and perform cybercrime. Here twist is the benefits of low latency,
global internet is undeniable, the satellite medium fundamentally disrupts the
foundational principles of the digital forensic investigation. In this part of
case study, we explored how traditional forensic strategies are failing in
orbit and why it failing?
Here is the most critical issue is
that of jurisdictional ambiguity. On terrestrial network, legal authorities can
force service providers to share their data, logs, and connection records.
However, in the satellite context, there is the situation becomes far more
complicated. If we saw an example like, a single data packets sent from a
Starlink terminal in Nigeria might be routed via a satellite other area,
downlink to a gateway in Italy, that process through a server cluster in
Germany and then exit into the public internet from Netherlands[12], [14]. In that such a case, there is five
different legal jurisdictions may have theoretical oversight over one simple
transaction, there for investigators this means that is issuing impact a lawful
request becomes a matter of transactional cooperation, that going to be more
difficult by diplomatic red tape, differing privacy laws, and the lack of any
sensitive unified forensic framework for orbital communications[7], [8]. Moreover, few of private corporations
are managed these satellite constellations, but that are not always bound to
cooperate, especially when operating in countries where data access is not that
much mandatory under local law[4].
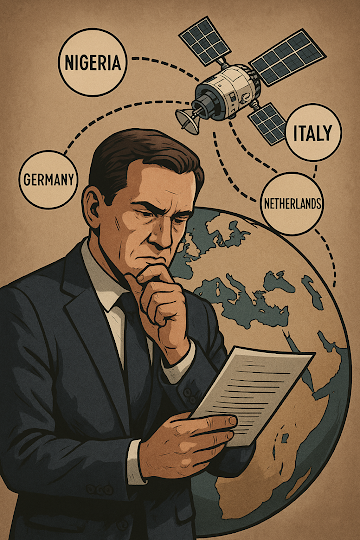
Figure
6:
Illustration representing the complexity of global satellite internet
routing and the resulting jurisdictional challenges for forensic
investigations.
|
As we all are move forward, and it is
highly increasingly clear that satellite internet technology has created a new
kind of digital terrain. Where criminals can hide behind the movement of
celestial bodies and perform cyber-attack through via satellite technology,
where forensic must evolve or risk becoming obsolete[4], [13]. Where forensic investigators not only
just looking under keyboards or may inside routers, also they are going to
scanning the orbital space, decoding the RF signals for tracing frequencies,
and chasing the digital criminals across over the world. In this emerging world
of technological paradigm, where traditional approaches must give way to
orbital strategies, and forensic investigation not only use software’s but also
include spectrum analyzers, satellite logs and cryptographic verification
model. The sky always has been extremely big, the reason why this situation in
more critical now and complicated too[4], [5].
Innovations on the Horizon — Building
a Forensic Future Beyond Earth
Despite
the huge challenges overcome in the digital forensic on satellite internet
technology, but hope is still existing. Across the global academia, law
enforcement, and private industry, researchers and engineers are continuously
trying to building the next generation of tools, protocols and frameworks to
investigate crime in borderless, orbital environment[15]. One of the most important areas of
innovation is RF signals, a technique that analyzes the subtle imperfections in
satellite terminals, radio emissions to uniquely identified a specific device. Much
like a human fingerprint, they can’t match each other due to manufacturing
variances and usages pattern. By cataloging and tracking these outflow,
forensic analyst and research team hardly trying to gain the ability to
satellite linked activities to a specific physical device, even also the
absence of logs and IP identifier[13], [14].
Figure
7:
RF fingerprinting used to trace satellite-linked devices in forensic
investigations.
|
As satellite internet uses are billon
of users, when its going from smart farms to autonomous ships, then need for
traceability, accountability and evidentiary integrity will become
non-negotiable. Here we need to upgrade our methodology, our techniques and
strategies, not just evolve tools and technology, but also need to update
imagination[16], [17].
In
the world where the internet falls from the sky, truth must rise with it.
About
the Author:
Mr. Srimanta Mondal
Research.srimanta@gmail.com
Gujarat University,
Department of Bio-Chemistry and Forensic, Cybersecurity and Digital Forensic
Science
Website: www.srimantamondal.in
LinkedIn:www.linkedin.com/in/srimanta-mondal-37b291184/
References:
[1] “The
Evolution of Humans | World Civilization.” Accessed: Jun. 29, 2025. [Online].
Available:
https://courses.lumenlearning.com/suny-hccc-worldcivilization/chapter/the-evolution-of-humans/
[2] “History
of Earth - Wikipedia.” Accessed: Jun. 29, 2025. [Online]. Available:
https://en.wikipedia.org/wiki/History_of_Earth
[3] “Indus
Valley Civilisation - Wikipedia.” Accessed: Jun. 29, 2025. [Online].
Available: https://en.wikipedia.org/wiki/Indus_Valley_Civilisation
[4] “Digital
Forensics and Cyber Crime Investigation | Recent Advances and.” Accessed: Jun.
29, 2025. [Online]. Available:
https://www.taylorfrancis.com/books/edit/10.1201/9781003207573/digital-forensics-cyber-crime-investigation-ahmed-abd-el-latif-lo-ai-tawalbeh-manoranjan-mohanty-brij-gupta-konstantinos-psannis
[5] “(PDF)
Emerging Trends in Digital Forensics : Investigating Cybercrime.” Accessed:
Jun. 29, 2025. [Online]. Available:
https://www.researchgate.net/publication/389631795_Emerging_Trends_in_Digital_Forensics_Investigating_Cybercrime
[6] “SATELLITE
FORENSICS - eForensics.” Accessed: Jun. 29, 2025. [Online]. Available:
https://eforensicsmag.com/product/satellite-forensics/
[7] “Starlink
- Wikipedia.” Accessed: Jun. 29, 2025. [Online]. Available: https://en.wikipedia.org/wiki/Starlink
[8] “Elon
Musk attacks South African government, claims ‘Starlink is not allowed to
operate in South Africa because…’ - The Times of India.” Accessed: Jun. 29,
2025. [Online]. Available: https://timesofindia.indiatimes.com/technology/social/elon-musk-attacks-south-african-government-claims-starlink-is-not-allowed-to-operate-in-south-africa-because/articleshow/118791502.cms
[9] “Starlink
in the Russian-Ukrainian War - Wikipedia.” Accessed: Jun. 29, 2025. [Online].
Available: https://en.wikipedia.org/wiki/Starlink_in_the_Russian-Ukrainian_War
[10] “Cybersecurity and Cyber Forensics for Smart Cities: A
Comprehensive Literature Review and Survey.” Accessed: Jun. 29, 2025.
[Online]. Available: https://www.mdpi.com/1424-8220/23/7/3681
[11] K. Kim, I. M. Alshenaifi, S. Ramachandran, J. Kim, T. Zia, and
A. Almorjan, “Cybersecurity and Cyber Forensics for Smart Cities: A
Comprehensive Literature Review and Survey,” Sensors 2023, Vol. 23, Page
3681, vol. 23, no. 7, p. 3681, Apr. 2023, doi: 10.3390/S23073681.
[12] “International Journal of Electronic Security and Digital
Forensics (IJESDF) Inderscience Publishers - linking academia, business and
industry through research.” Accessed: Jun. 29, 2025. [Online]. Available:
https://www.inderscience.com/info/ingeneral/forthcoming.php?jcode=ijesdf
[13] “Researching Cyber Security of Small Satellites | CybExer
Technologies.” Accessed: Jun. 29, 2025. [Online]. Available:
https://cybexer.com/case-studies/researching-cyber-security-of-small-satellites-using-digital-twin-and-cyber-range-technology
[14] “Cybercrime Module 6 Key Issues: References.” Accessed: Jun. 29,
2025. [Online]. Available:
https://www.unodc.org/e4j/zh/cybercrime/module-6/key-issues/references.html
[15] “Satellite Cybersecurity, 10-R6221 | Southwest Research
Institute.” Accessed: Jun. 29, 2025. [Online]. Available:
https://www.swri.org/what-we-do/internal-research-development/2022/earth-space/satellite-cybersecurity-10-r6221
[16] “Cybercrime - Wikipedia.” Accessed: Jun. 29, 2025. [Online].
Available: https://en.wikipedia.org/wiki/Cybercrime
[17] D. of Justice, O. of Justice Programs, and N. Institute of
Justice, “Special REPORT Electronic Crime Scene Investigation: A Guide for
First Responders, Second Edition,” 2001. [Online]. Available:
www.ojp.usdoj.gov/nij


.png)
.png)